Telnet basically stands for “teletype network”. It is an old network protocol that works on the application layer of the OSI model. It connects to a remote system using the internet or LAN to provide a text-based communication using a virtual terminal. Generally, telnet is used to establish a connection to transmission control protocol (TCP) using port 23 where the telnet server (telnetd) application is listening. This protocol was developed in 1969.
[alert color=”red”] WARNING: Nowadays It is not recommended to use the telnet especially on an open network like the internet because by default data sent over the connection including password and other confidential information is not encrypted so the data transmitted can be easily intercepted by a hacker and misused. You should prefer to use SSH (Secure Shell) instead of using telnet, which is an encrypted, more secure protocol and serves the same purpose.[/alert]
How to Install Telnet Server on Linux?
Telnet client makes requests to the remote machine where the telnet server application is installed. This server application listens to all the requests made by a client. Based on the distribution that you are using, execute the given command in the terminal-
In a Debian based distribution, use –
sudo apt-get install telnetd -y
In RPM-based Linux distributions, use –
sudo yum install telnet telnet-server -y
How to run and auto restart the Telnet services on system startup?
Once installed, you can start and enable telnet services so that in case of server restarts, the telnet services get started automatically.
Use the following command to start the services in centos, RHEL, and other distributions that use RPM as the package manager-
systemctl start telnet.socket
And to enable the services
systemctl enable telnet.socket
Modify Firewall Settings to allow communication on port 23
By default firewall blocks port 23 which is the default port used by telnet. This port is blocked by firewall because telnet protocol is not considered secure to use it transmits data in unencrypted form. To use telnet service we have to modify the firewall settings to allow the port 23. To make the changes use the following command-
firewall-cmd --permanent --add-port=23/tcp
And reload the firewall to make the changes effective by using given command-
firewall-cmd --reload
How to Check if Telnet is running or not?
To check the status of the telnet server execute the following command into your terminal –
In CentOS, RHEL and similar distributions –
systemctl status telnet.socket
In Debian based distributions-
systemctl status inetd
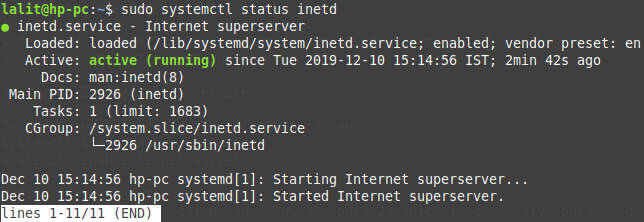
As you can see above the server is running actively and it is ready to take the connection request of a client.
Login To The Telnet Server
Now you can access the server remotely by using telnet. Before accessing it remotely if required create a new user and secure it with a password. Now execute the following command to get connected and login to the remote system.
telnet server_IP_address
For example-
telnet localhost

As soon as you execute the command above it gets connected to the server and asks you to enter username and password enter it and press return key. Now the command line interface of the remote system is accessible you can execute a command in it.
Why Use Telnet when it is not secure?
This question is obvious at least in today’s world where secure communication has become immensely important. In today’s world where everyone is using SSH and all other secure means of communication what purpose the Telnet serves in terms of communication, one may think!
Telnet is still used in the development environments which is run on a local network. Well, it is dangerous to use telnet in public networks where everyone can see the data. But you can use the telnet to communicate between devices in a local cable network or on a wifi network where you have the control of the network.
You are the user, so you can best decide when to use Telnet and when not to based on an understanding of the pros and cons of this communication protocol.
That’s all for now on the topic of Telnet. Now I hope this gives you a basic understanding of how and why to use Telnet. If you would like to say something on the topic or have a query regarding it please write to us in the comments below.